Home Tags Posts tagged with "cybercriminals"
cybercriminals
Grum, a botnet which experts believe sent out 18% of the world’s spam email, has been shut down, a security firm said.
Grum’s control servers were mainly based in Panama, Russia and Ukraine.
Security company FireEye and spam-tracking service SpamHaus worked with local internet service providers (ISPs) to shut down the illegal network.
A botnet is a network of computers that has been hijacked by cybercriminals, usually by using malware.
“Grum’s takedown resulted from the efforts of many individuals,” wrote Atif Mushtaq, a security researcher with FireEye.
“This collaboration is sending a strong message to all the spammers: Stop sending us spam. We don’t need your cheap Viagra or fake Rolex.”
Atif Mushtaq wrote that on Monday he learned that a Dutch server involved in Grum had been shut down. He said it “at least made a dent” in the botnet.
Grum botnet is believed to send out 18 percent of the world's spam email
On Tuesday, the command and control servers (CnCs) in Panama had been shut down.
“This good news was soon followed by some bad news,” he explained.
“After seeing that the Panamanian server had been shut down, the bot herders moved quickly and started pointing the rest of the CnCs to new secondary servers in Ukraine.
“So at one point, I was thinking that all we needed was to take down one Russian server, but right in front of my eyes, the bot herders started pointing their botnet to new destinations.”
He noted that in the past Ukraine has been something of a “safe haven” for bot herders.
“Shutting down any servers there has never been easy.”
Disabling Grum is just one of many high-profile efforts to neutralise botnets worldwide.
Russian Georgiy Avanesov was in May sentenced to four years in jail for being behind the Bredolab botnet which was believed to have been generating more than £80,000 a month in revenue.
Microsoft has been working to disrupt Zeus, another huge network responsible for, researchers said, millions of pounds in theft.
FireEye collaborated with other experts in the worldwide security industry to apply pressure to local ISPs to suspend the illegal operation.
Atif Mushtaq said more than 20,000 computers were still part of the botnet, but that without the active CnCs they would soon be rendered ineffective.
Grum’s closure was an encouraging development in clamping down on botnets across the world, he said.
“When the appropriate channels are used, even ISPs within Russia and Ukraine can be pressured to end their cooperation with bot herders.
“There are no longer any safe havens. Most of the spam botnets that used to keep their CnCs in the USA and Europe have moved to countries like Panama, Russia, and Ukraine thinking that no one can touch them in these comfort zones.
“We have proven them wrong this time. Keep on dreaming of a junk-free inbox.”
A Microsoft researcher says Smartphones running Google’s Android software have been hijacked by an illegal botnet.
Botnets are large illegal networks of infected machines – usually desktop or laptop computers – typically used to send out masses of spam email.
Researcher Terry Zink said there was evidence of spam being sent from Yahoo mail servers by Android devices.
Microsoft’s own platform, Windows Phone, is a key competitor to Android.
The Google platform has suffered from several high-profile issues with malware affected apps in recent months.
The official store – Google Play – has had issues with fake apps, often pirated free versions of popular paid products like Angry Birds or Fruit Ninja.

Smartphones running Google's Android software have been hijacked by an illegal botnet
This latest discovery has been seen as a change of direction for attackers.
“We’ve all heard the rumors,” Terry Zink wrote in a blog post.
“But this is the first time I have seen it – a spammer has control of a botnet that lives on Android devices.
“These devices login to the user’s Yahoo Mail account and send spam.”
He said analysis of the IP addresses used to send the email revealed the spam had originated from Android devices being used in Chile, Indonesia, Lebanon, Oman, Philippines, Russia, Saudi Arabia, Thailand, Ukraine, and Venezuela.
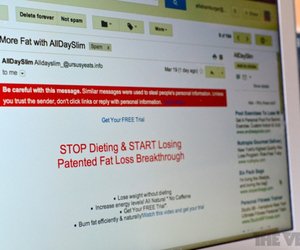
As is typical, the spam email looks to tempt people into buying products like prescription drugs.
Security expert Graham Cluley, from anti-virus firm Sophos, said it was highly likely the attacks originated from Android devices, given all available information, but this could not be proven.
This was the first time smartphones had been exploited in this way, he said.
“We’ve seen it done experimentally to prove that it’s possible by researchers, but not done by the bad guys,” he said.
“We are seeing a lot of activity from cybercriminals on the Android platform.
“The best thing you can do right now is upgrade your operating system, if that’s possible.
“And before you install apps onto your device, look at the reviews, because there are many bogus apps out there.”
Google said it did not respond to queries about specific apps but was working to improve security on the Android platform.
“We are committed to providing a secure experience for consumers in Google Play, and in fact our data shows between the first and second halves of 2011, we saw a 40% decrease in the number of potentially malicious downloads from Google Play,” a spokesman said.
“Last year we also introduced a new service into Google Play that provides automated scanning for potentially malicious software without disrupting the user experience or requiring developers to go through an application approval process.”
Russian researchers have discovered a complex targeted cyber-attack that collected private data from countries such as Israel and Iran.
Russian security firm Kaspersky Labs said they believed the malware, known as Flame, had been operating since August 2010.
The company said it believed the attack was state-sponsored, but could not be sure of its exact origins.
They described Flame as “one of the most complex threats ever discovered”.
Research into the attack was carried out in conjunction with the UN’s International Telecommunication Union.

Russian security firm Kaspersky Labs said they believed the malware, known as Flame, had been operating since August 2010
In the past, targeted malware – such as Stuxnet – has targeted nuclear infrastructure in Iran.
Others like Duqu have sought to infiltrate networks in order to steal data.
This new threat appears not to cause physical damage, but to collect huge amounts of sensitive information, said Kaspersky’s chief malware expert Vitaly Kamluk.
“Once a system is infected, Flame begins a complex set of operations, including sniffing the network traffic, taking screenshots, recording audio conversations, intercepting the keyboard, and so on,” he said.
More than 600 specific targets were hit, Vitaly Kamluk said, ranging from individuals, businesses, academic institutions and government systems.
Iran’s National Computer Emergency Response Team posted a security alert stating that it believed Flame was responsible for “recent incidents of mass data loss” in the country.
Vitaly Kamluk said the size and sophistication of Flame suggested it was not the work of independent cybercriminals, and more likely to be government-backed.
He explained: “Currently there are three known classes of players who develop malware and spyware: hacktivists, cybercriminals and nation states.
“Flame is not designed to steal money from bank accounts. It is also different from rather simple hack tools and malware used by the hacktivists. So by excluding cybercriminals and hacktivists, we come to conclusion that it most likely belongs to the third group.”
Among the countries affected by the attack are Iran, Israel, Sudan, Syria, Lebanon, Saudi Arabia and Egypt.
“The geography of the targets and also the complexity of the threat leaves no doubt about it being a nation-state that sponsored the research that went into it,” Vitaly Kamluk said.
The malware is capable of recording audio via a microphone, before compressing it and sending it back to the attacker.
It is also able to take screenshots of on-screen activity, automatically detecting when “interesting” programs – such as email or instant messaging – were open.
Kaspersky’s first recorded instance of Flame is in August 2010, although it said it is highly likely to have been operating earlier.
Prof. Alan Woodward, from the Department of Computing at the University of Surrey said the attack is very significant.
“This is basically an industrial vacuum cleaner for sensitive information,” he said.
He explained that unlike Stuxnet, which was designed with one specific task in mind, Flame was much more sophisticated.
“Whereas Stuxnet just had one purpose in life, Flame is a toolkit, so they can go after just about everything they can get their hands on.”
Once the initial Flame malware has infected a machine, additional modules can be added to perform specific tasks – almost in the same manner as adding apps to a smartphone.