Flame malware makers send suicide command to infected computers
Flame malware’s makers have sent a “suicide” command that removes it from some infected computers.
Security firm Symantec caught the command using booby-trapped computers set up to watch Flame’s actions.
Flame came to light after the UN’s telecoms body asked for help with identifying a virus found stealing data from many PCs in the Middle East.
New analysis of Flame reveals how sophisticated the program is and gives hints about who created it.
Like many other security firms Symantec has kept an eye on Flame using so-called “honeypot” computers that report what happens when they are infected with a malicious program.
Described as a very sophisticated cyber-attack, Flame targeted countries such as Iran and Israel and sought to steal large amounts of sensitive data.
Earlier this week Symantec noticed that some Flame command and control (C&C) computers sent an urgent command to the infected PCs they were overseeing.
Flame’s creators do not have access to all their C&C computers as security firms have won control of some of them.
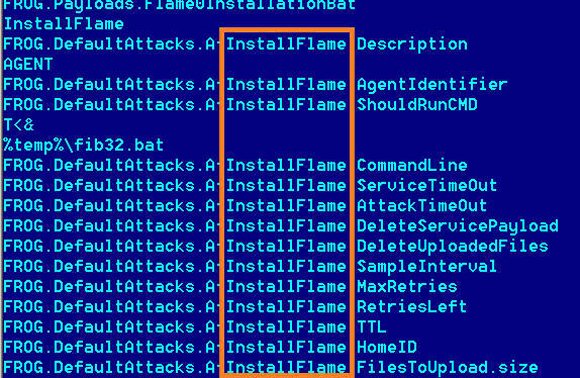
The “suicide” command was “designed to completely remove Flame from the compromised computer”, said Symantec.
The command located every Flame file sitting on a PC, removed it and then overwrote memory locations with gibberish to thwart forensic examination.
“It tries to leave no traces of the infection behind,” wrote the firm on its blog.
Analysis of the clean-up routine suggested it was written in early May, said Symantec.
At the same time, analysis of the inner workings of Flame reveal just how sophisticated it is.
According to cryptographic experts, Flame is the first malicious program to use an obscure cryptographic technique known as “prefix collision attack”. This allowed the virus to fake digital credentials that had helped it to spread.
The exact method of carrying out such an attack was only demonstrated in 2008 and the creators of Flame came up with their own variant.
“The design of this new variant required world-class cryptanalysis,” said cryptoexpert Marc Stevens from the Centrum Wiskunde & Informatica (CWI) in Amsterdam in a statement.
The finding gives support to claims that Flame must have been built by a nation state rather than cybercriminals. It is not clear yet which nation created the program.